You can configure Scanner parameters, and change default actions for detected threats. The default settings are optimal for most cases. Do not change them unnecessarily.
To open file scan options
1.Open Dr.Web menu ![]() , then select Security Center.
, then select Security Center.
2.Make sure Dr.Web operates in administrator mode (the lock at the bottom of the program window is open ![]() ). Otherwise, click the lock
). Otherwise, click the lock ![]() .
.
3.At the top of the program window, click .
4.A product main settings window opens. Select Scanner at the left of the window.
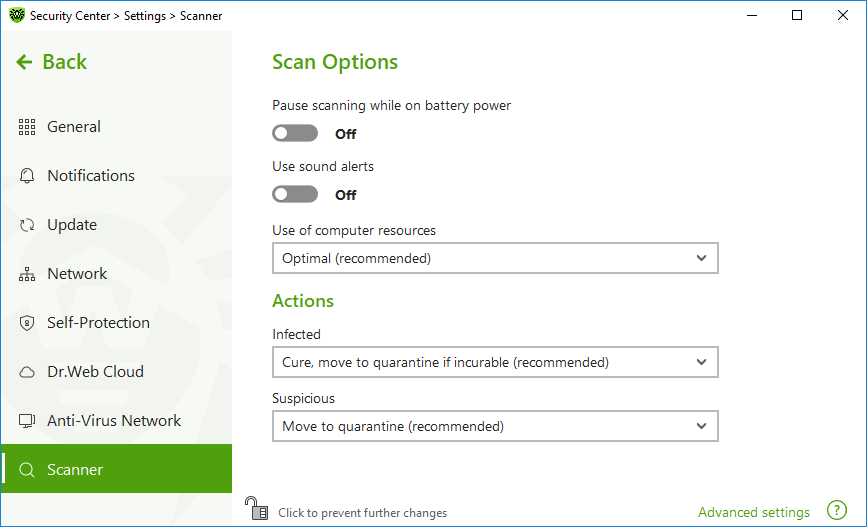
Figure 37. Scanner settings
Scan Options
In this group, you can configure general parameters of Dr.Web Scanner operation.
•Pause scanning while on battery power. Enable this option to pause scanning when switching to battery mode. If the grid power is restored within 30 seconds, the scan will resume automatically. Option is disabled by default.
•Use sound alerts. Enable this option for Dr.Web Scanner to use sound alerts for every event of detecting or neutralizing a threat. Option is disabled by default.
•Use of computer resources. This option limits the use of computer resources by Dr.Web Scanner. The default value is optimal for most cases.
Actions
In this setting group, you can specify Scanner reaction to detection of infected or suspicious files and malware.
For different types of compromised objects, actions are assigned separately from the respective drop-down lists:
•Malicious—objects with a known and (presumably) curable threat.
•Suspicious—objects suspected to contain threats.
•Objects that pose potential threat (riskware).
By default, Scanner attempts to cure files with a known and potentially curable threat. Scanner moves the other most dangerous objects to Quarantine. You can change reaction of Scanner to detection of each type of malware separately. Set of available reactions depends on the threat type. The default actions are optimal and marked as recommended.![]() More about reactions
More about reactions
You can select one of the following actions for detected threats:
|
|
Threats within complex objects (archives, email attachments, file containers) cannot be processed individually. For such threats, Dr.Web Scanner applies an action selected for this type of a complex object. |
Additional options
To open advanced settings, click the Advanced settings link in the Scan Options window Figure Scanner settings.
You can disable check of containers, archives, and email files. This option is enabled by default.
You can also select one of the following actions for Scanner to perform once scanning is completed:
•Do not apply action. Scanner will display the list of detected threats.
•Neutralize detected threats. Scanner will neutralize threats automatically.
•Neutralize detected threats and shut down the computer. Scanner will shut down the computer once threats are automatically neutralized.